Okay, deep breath, let's get this over with. In the grand act of digital self-sabotage, we've littered this site with cookies. Yep, we did that. Why? So your highness can have a 'premium' experience or whatever. These traitorous cookies hide in your browser, eagerly waiting to welcome you back like a guilty dog that's just chewed your favorite shoe. And, if that's not enough, they also tattle on which parts of our sad little corner of the web you obsess over. Feels dirty, doesn't it?
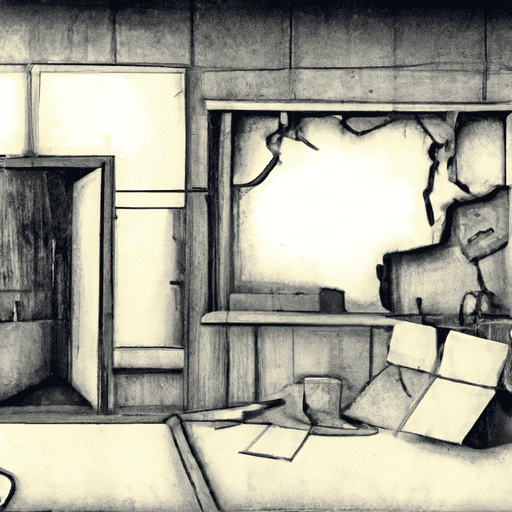
Ghost Tech: How Malicious Actors Exploit Windows Container Isolation Framework
Discover how malicious actors are turning into tech ghosts, bypassing endpoint security solutions by exploiting the Windows Container Isolation Framework. It’s a security risk that’s there but not quite there, just like a ghost.